Share this post

Imagine an organization experiences a cybersecurity incident. Sensitive data is exposed. Customers grow anxious. Regulators begin asking questions. Media coverage intensifies. Reputation suffers. It feels like a nightmare.
But the breach itself is often only the first phase. Once attackers obtain internal information, they gain strategic intelligence: employee emails, customer records, login credentials, or operational details. Your company, your staff, and your customers can become long-term targets for carefully crafted phishing campaigns built on that stolen data.
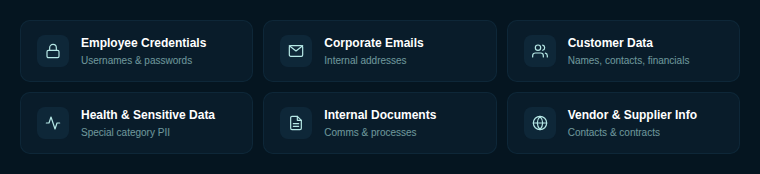
Breached data refers to any information accessed, disclosed, or extracted without authorization. In corporate environments, this typically includes credentials, corporate email addresses, customer contact and financial details, health or other sensitive personal data, internal documents, and vendor or supplier contact information.
Once exposed, such data often circulates on underground forums or criminal marketplaces. It may be aggregated into credential lists, used for automated login attempts, or analyzed to prepare targeted social engineering campaigns. Information that seems routine inside an organization becomes strategic intelligence in the hands of an attacker.
A breach creates immediate risk for the affected organization, but the impact frequently extends beyond it. Companies connected through partnerships, supplier agreements, shared systems, or customer relationships can also face elevated exposure.
For the breached organization, attackers may gain access to credentials, internal communications, and sensitive records. This can lead to account takeover, business email compromise, data exfiltration, and operational disruption. Even after technical containment, the stolen information may continue to be exploited. Public disclosure of the incident can further amplify risk, as attackers use the breach as a pretext to send fraudulent “security updates” or “verification” messages to employees and customers.
Organizations that have not experienced a direct breach may still become indirect victims. Attackers frequently impersonate the compromised company to target its partners. Messages referencing legitimate contracts, invoices, or joint projects can appear authentic because the business relationship is real. Trust becomes the attack vector.
If shared systems, API integrations, remote access portals were in place, compromised credentials from the affected company may be used to attempt lateral access. Even standard communications from the breached partner should be treated cautiously until its security posture is confirmed stable. It is also important to acknowledge a practical challenge: not all suppliers immediately inform partners about incidents, and some organizations may not even detect that they have been compromised. This lack of visibility increases uncertainty and underscores the need for independent monitoring and proactive risk management.
Security planning must therefore account not only for internal breaches but also for supply chain exposure. PayPal has confirmed a data breach tied to its PayPal Working Capital loan application that exposed customer data for up to six months and has issued breach notification letters to affected users. When financial data is exposed for months before detection, attackers have ample time to craft highly targeted phishing campaigns - fraudulent loan confirmations, fake account alerts, or payment verification requests that reference real customer details.
The Dutch telecommunications provider Odido publicly confirmed a cyber incident that exposed personal data of more than 6.2 million customers. A breach of this scale provides attackers with a massive contact database for phishing at volume. Customers who learn about the incident through media coverage become especially vulnerable to fake "security update" or "identity verification" emails that exploit their concern.
Figure Technology, the fintech lending company, confirmed it experienced a data breach after a hacker used social engineering to trick an employee into granting system access, allowing files to be downloaded. Later, the group ShinyHunters claims it released 2.5 GB of stolen data after a ransom was refused, and researchers link the incident to a broader 2026 campaign targeting organizations using Okta’s SSO through vishing attacks. This case illustrates the full cycle: a social engineering attack causes the breach, and the stolen data then enables further social engineering against partners and customers. The vishing vector used to gain initial access is exactly the type of attack that organizations must train their employees to recognize, before it leads to downstream compromise.
Phishing becomes far more effective when attackers possess real, contextual information. With breached data, fraudulent emails can include accurate employee names, job titles, vendor details, project references, and even copied email signatures. These elements reduce suspicion because the message aligns with known business processes. Attackers may send convincing password reset requests, billing notifications or customer service responses that mirror legitimate communication styles. Because the contact details are genuine, the messages appear credible. In this way, breached data transforms phishing from generic spam into precise social engineering.
When an incident occurs, whether internally or within a partner organization, the response must go beyond technical containment. Defensive strategy should address both immediate compromise and the risk of secondary phishing campaigns. Preparation begins with strong identity controls. Multi-factor authentication should be enforced consistently, especially for email, remote access, and administrative accounts. Shared credentials and integrations with third parties should be reviewed and restricted to the minimum necessary access.
Monitoring must be intensified after any known breach. This includes reviewing login anomalies, unexpected mailbox rules, unusual financial requests, and abnormal data transfers. Third-party access should be reassessed immediately when a partner reports an incident.
Equally important is the preparation for phishing scenarios. Organizations should study common attack patterns used after breaches, such as fake security notifications, invoice redirection attempts, or impersonation of executives. Clear internal rules should define how financial requests are verified, how password resets are handled, and how suspicious messages are reported. These procedures must be practiced, not merely documented.
Employee awareness programs should include realistic phishing simulations that reflect breach-related scenarios. Staff should understand that attackers may exploit urgency, fear, or references to real incidents. Training should reinforce verification culture: confirm before clicking, confirm before transferring funds, confirm before sharing credentials.
Even strong security does not guarantee isolation from risk. Through partners, suppliers, and shared systems, your organization can become involved in an incident without being directly breached. Stolen information will be used to target your employees and customers with convincing, context-rich phishing attacks. The examples above show that this is not theoretical, it is already happening, at scale, across industries. Monitoring partner incidents, preparing for realistic phishing scenarios, and building a culture of verification are not optional extras. They are the difference between catching a well-crafted attack and falling for one. Because the question is no longer if your organization will be targeted with breach-informed phishing, it's whether your people will be ready when it happens.
When attackers obtain breached data such as employee credentials, customer records, or internal communications, they use this information to craft highly targeted phishing emails. These messages reference real names, job titles, projects, or business relationships, making them far more convincing than generic phishing attempts.
Yes. Attackers frequently use information from a breached organization to target its partners and suppliers. Messages referencing legitimate contracts, invoices, or shared projects can appear authentic because the underlying business relationship is real. Supply chain exposure is one of the most underestimated phishing risks.
The most valuable data for phishing includes corporate email addresses, login credentials, customer contact and financial details, internal documents, and vendor contact information. Even seemingly routine business data can become strategic intelligence for attackers.
Key defenses include enforcing multi-factor authentication, monitoring for login anomalies and unusual requests after known incidents, reviewing third-party access, and running realistic phishing simulations that reflect post-breach attack scenarios. Building a verification culture - where employees confirm requests before acting - is critical.
Phishing campaigns can start within hours of a breach becoming public. Attackers exploit urgency and fear by sending fake security notifications or account verification requests while victims are still reacting to the news.